3 minutes process to
an eternal legacy
From creating your first vault to the moment your loved ones receive your legacy — every step is simple, private, and permanent.
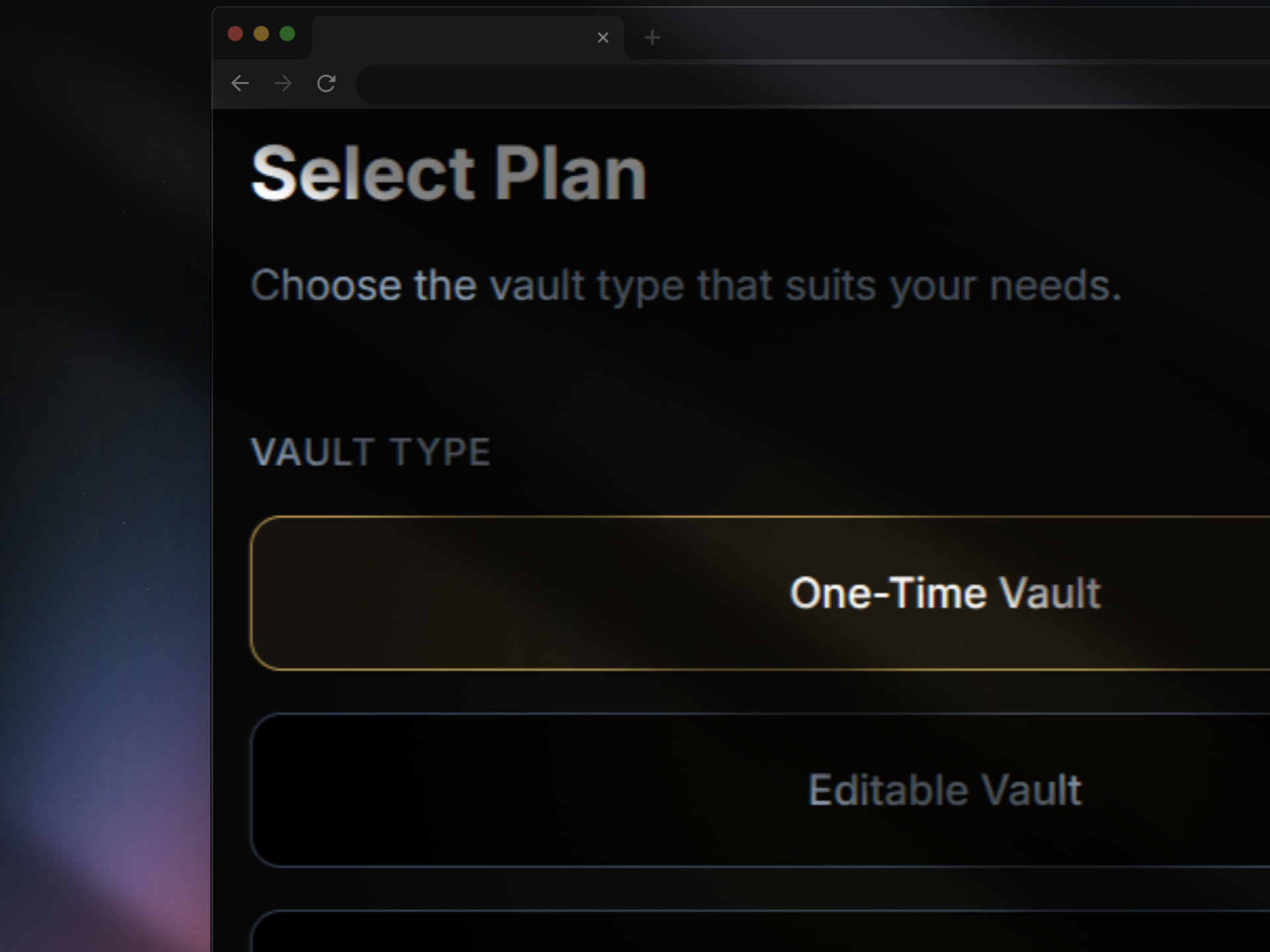
Select Your Vault Type
Choose the vault that fits your needs. Whether you want a static immutable record, an editable archive, or an extra large storage Editable Plus vault — each type is designed for a different legacy use case.
- Immutable Vault — one-time permanent, tamper-proof record
- Editable Vault — update your legacy anytime
- Editable+ Vault — Extra large storage, for media inheritance
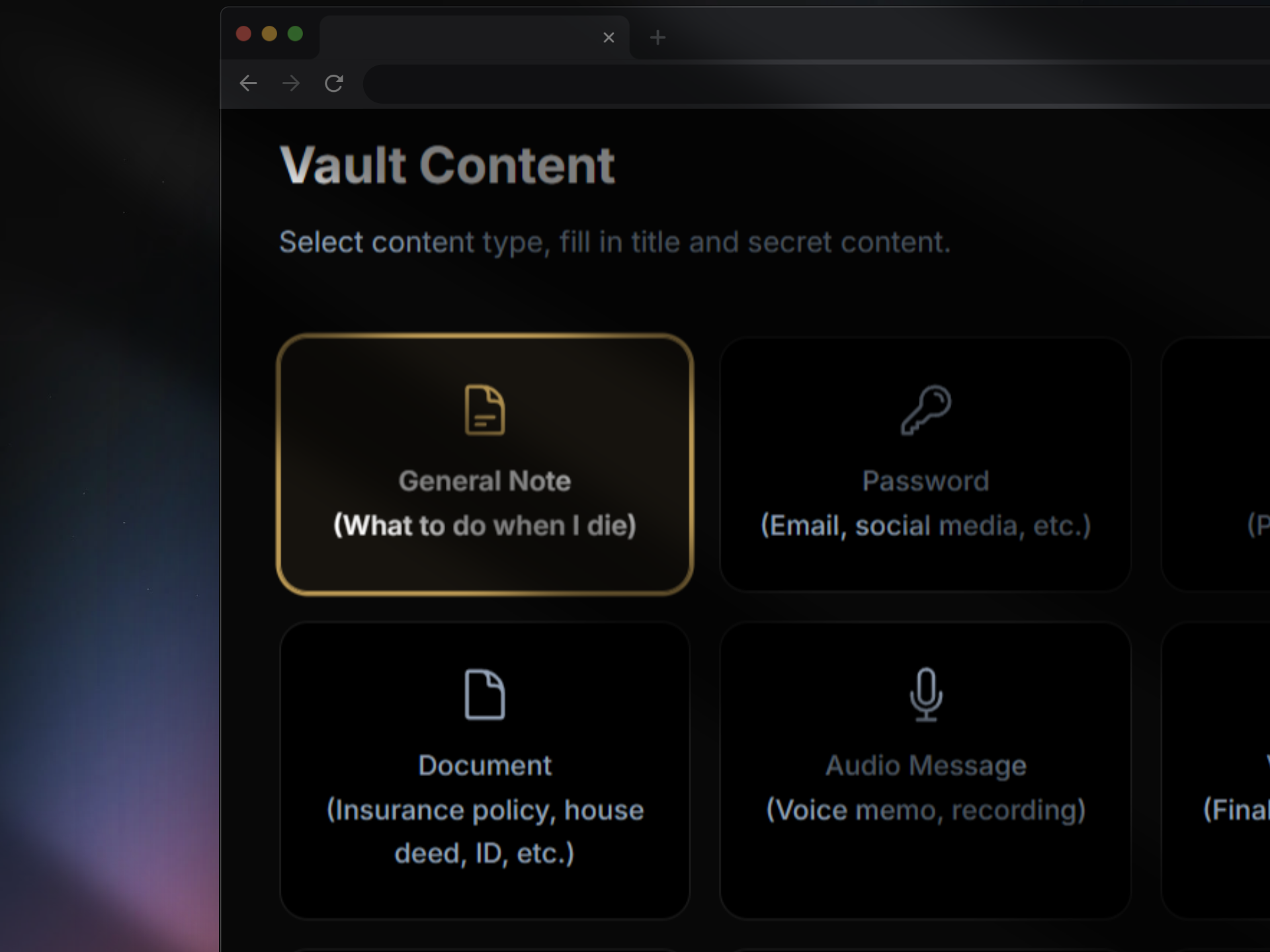
Select Vault Content
Add what matters most — documents, messages, crypto credentials, passwords, photos, and personal letters. Everything is encrypted on your device before it's ever uploaded.
- Documents & legal files
- Crypto wallet keys & seed phrases
- Personal messages & video notes
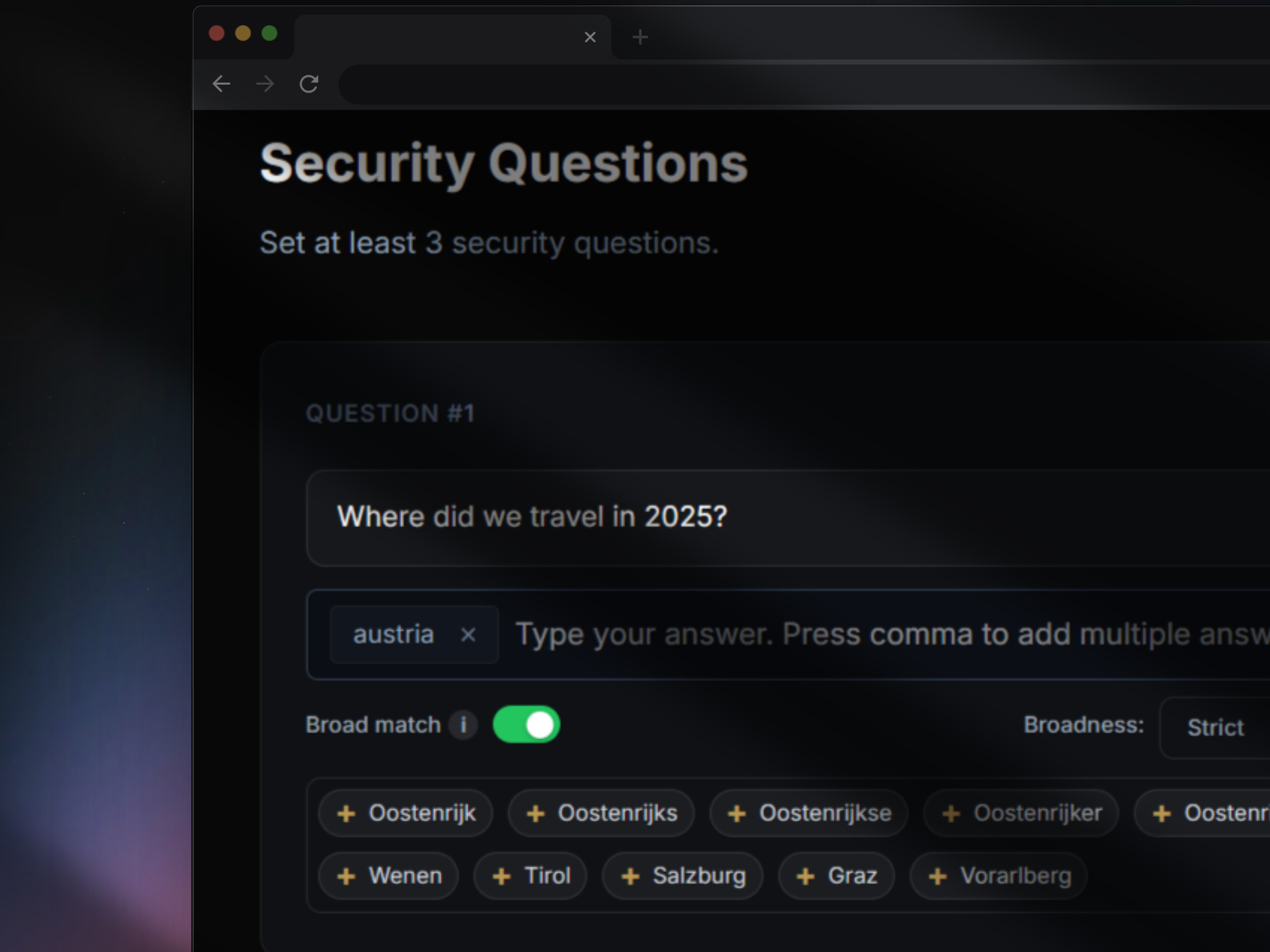
Create Security Questions
Define secret questions only your intended recipients can answer. This adds a human layer of verification — ensuring the right person accesses the right content, even without a password.
- Set custom questions per vault
- Multiple-choice or free-text answers
- Combined with cryptographic key delivery
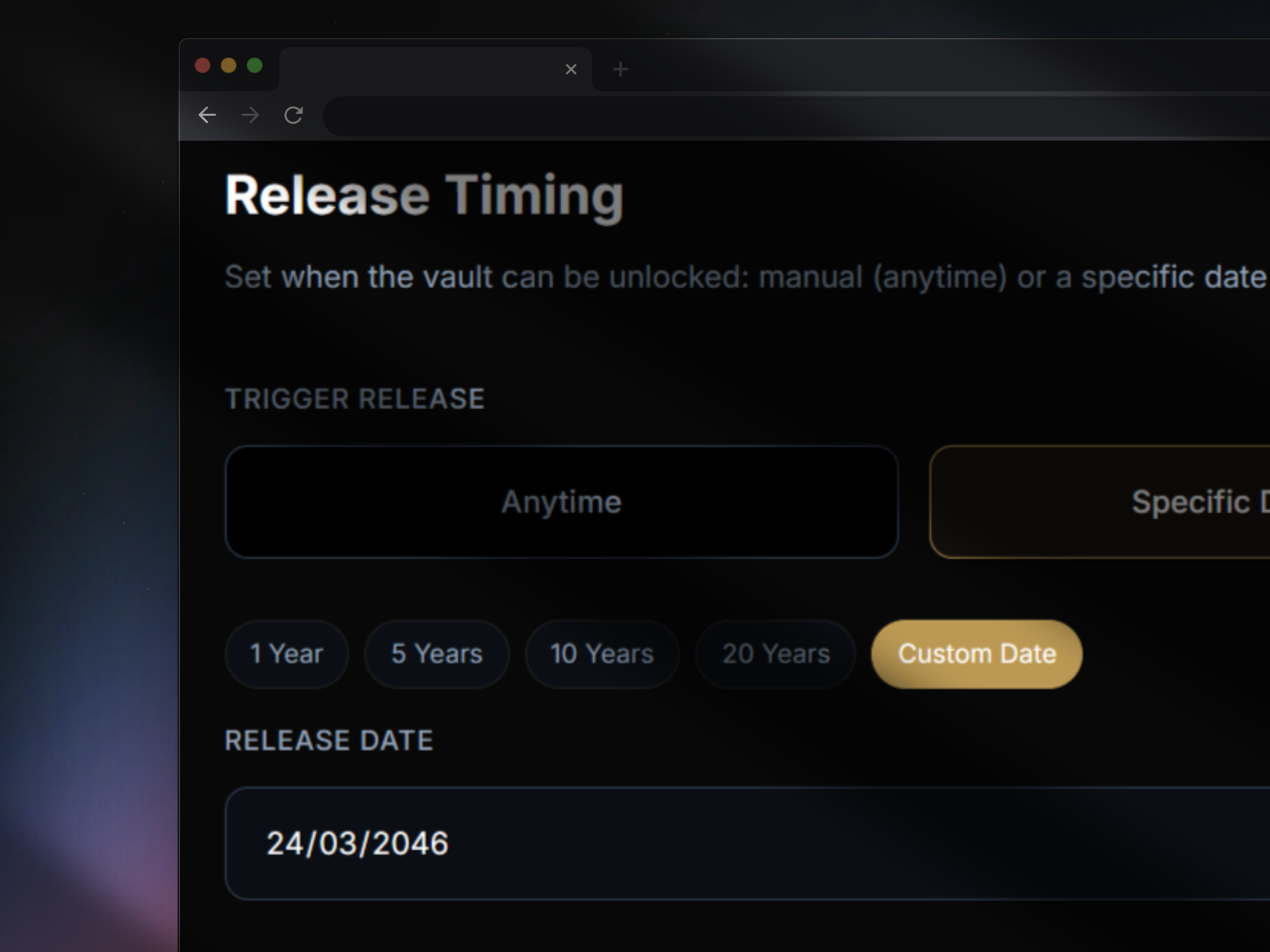
Select a Trigger & Release Date
Decide when and how your vault unlocks. Choose a specific date, a period of inactivity, or a verified life event. You remain in full control until the trigger is met.
- Time-based — unlock after a set date
- Inactivity — unlock after no check-in
- Event-based — unlock upon a verified event
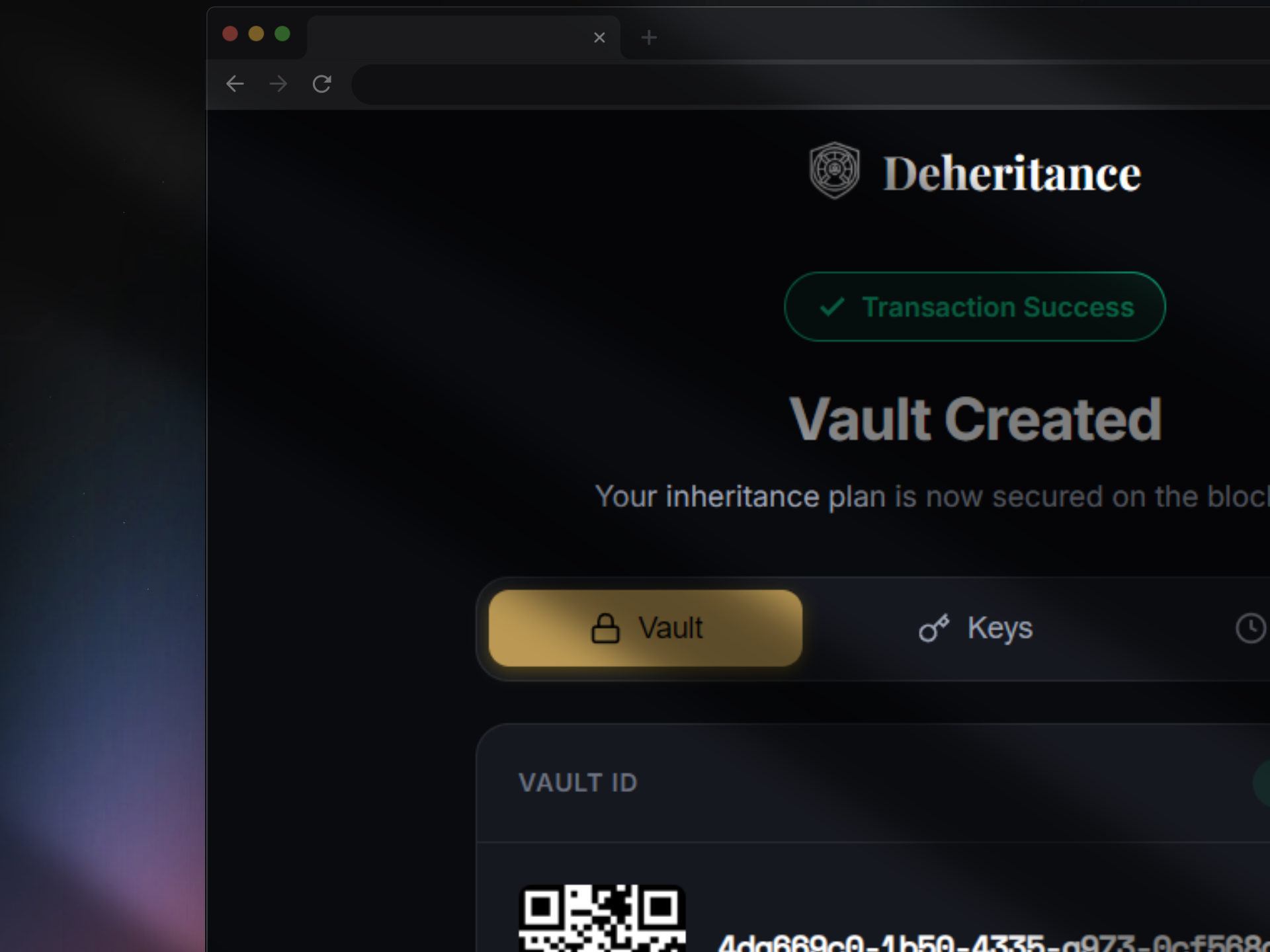
Vault & Keys Created
Your vault is sealed, encrypted, and stored permanently on the decentralised web. A unique set of cryptographic keys is generated — a fully backup for you as the owner, or separate keys for each of your beneficiaries.
- Stored on-chain — permanently
- Quantum-proof encryption, zero-knowledge architecture
- Share the fraction keys via email or encypted chat message
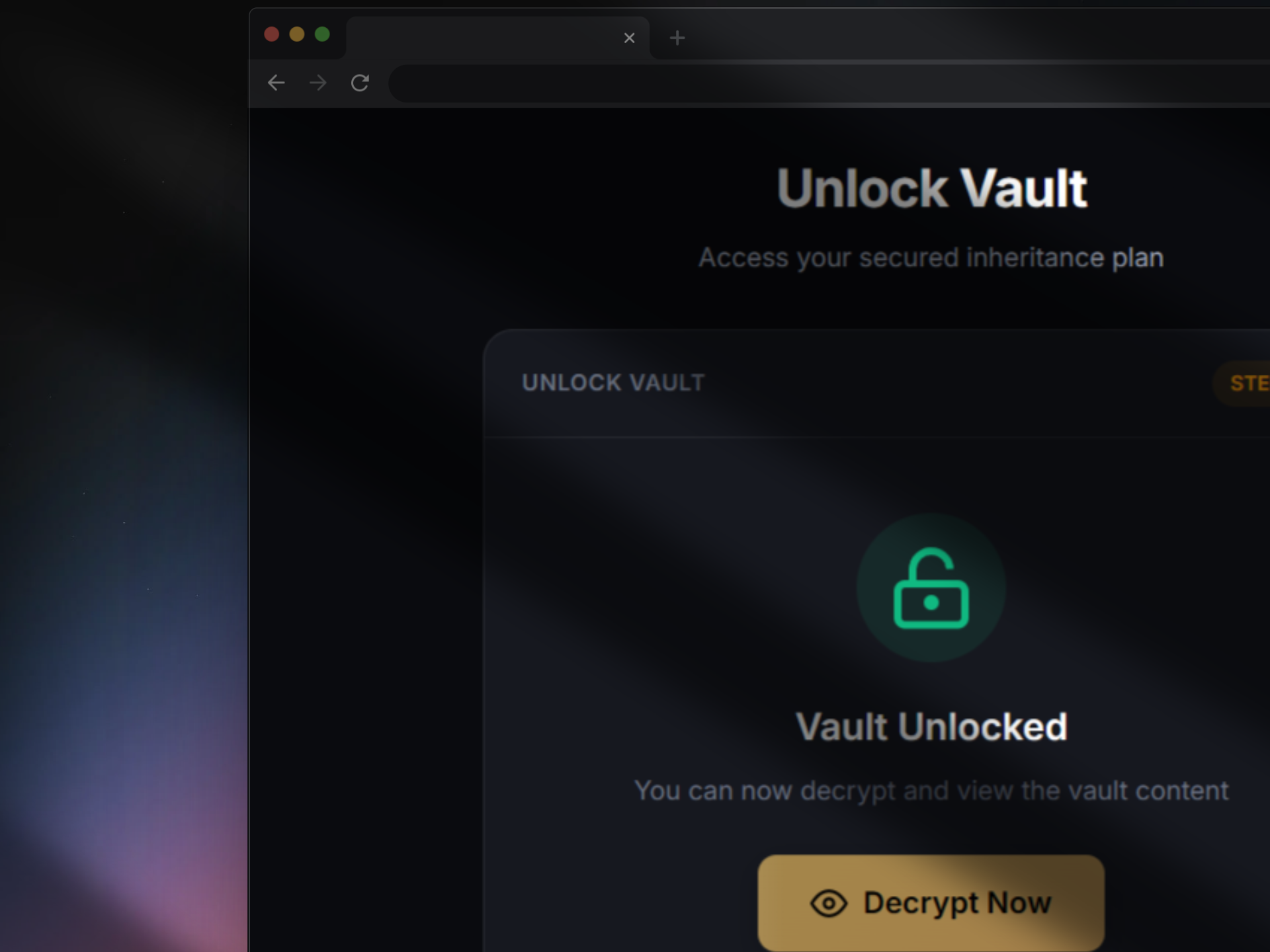
Unlock Vault
Unlock the vault when the trigger is met. Your beneficiaries use their fraction key to unlock and access the vault.
- Unlock via web app, Chrome Extension or open-source tool
- Security questions confirm identity before access
- Access vault using 3-5 threshold fraction keys
Ready to Create Your Vault?
It takes less than 3 minutes to secure your legacy forever.
Create a Vault View Pricing →